The Five Eyes, the combined intelligence services of Australia, Canada, New Zealand, the United Kingdom, and the United States, issued an alert on 20 April 2022 warning of increased ‘malicious cyber activity’ as a result of Russia’s invasion of Ukraine.
This follows the 21 March 2022 statement by President Biden, in which he highlighted the potential for Russia to target the US with malicious cyber activity.
The focus is ‘critical national infrastructure’ – things like water and power supply, public health services, and telecommunications – but acknowledges the vulnerabilities that can exist where remote access is used without good security. Of course, this issue affects a much wider range of organisations.
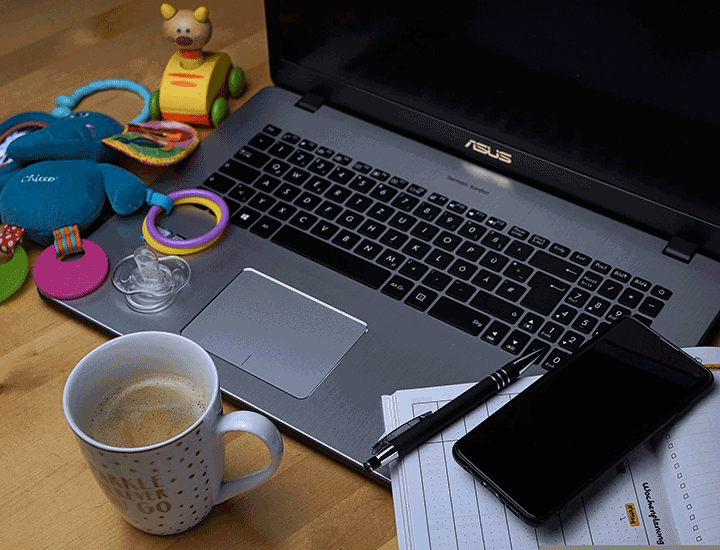
Is remote working less secure?
Whether working from home is less secure and working in the office is more secure has been something of a debate since 2020, when national lockdowns meant remote working was a necessity for many people.
Either way, remote working, or hybrid working, does at least create some cyber security questions that we need to consider.
In the context of the Five Eyes alert, there are a couple of areas to think about:
- Remote access. If everyone is in the office, there is no need for remote access (though for this to be true from a security perspective, the technologies enabling remote access need to turned off, rather than simply not used, otherwise the route for attackers remains). This reduces the ‘attack surface.
- Network security. It tends to be the case that business networks (including internet connections) have stronger security in place than home networks (e.g., well-managed firewalls, network monitoring etc.) so there are potentially increased risks with remote working.
However, for many organisations it’s neither attractive nor realistic to consider everyone being back in the office, all of the time. Hybrid working, where it’s not a case of ‘one or the other’, but a blend of both, looks like being a sensible medium-term approach in a lot of cases. Our Think IT ‘Hybrid Working’ Insights article is worth a look here, covering various important technology and security aspects.
How do I reduce the risk of cyber attack?
The alert, or ‘joint Cybersecurity Advisory’, specifically mentions four ‘mitigations’: controls that can be put in place to reduce the likelihood and/or impact of cyber attacks:
- Updating software
- Enforcing Multi-Factor Authentication (MFA)
- Securing and monitoring RDP
- Providing end-user awareness training
Updating software features in almost all security advice; software vendors (like Microsoft, Apple and Google) are discovering issues in software all the time, and developing ‘fixes’ or ‘patches’ for these issues all the time. Many systems now support automatic updates, so it’s generally a good idea to ensure this is turned on and working correctly.
Multi-Factor Authentication (MFA) is becoming another key security recommendation, and one that most people that do any online banking are already familiar with. It’s now a Cyber Essentials requirement, and increasingly insurers are also checking that MFA is in place for access to cloud services (like Microsoft 365) and remote access to business systems.
Remote access, particularly using Remote Desktop Protocol (RDP) is commonly targeted by attackers (and as the alert noted, “RDP exploitation is one of the top initial infection vectors for ransomware, and risky services, including RDP, can allow unauthorized access to your session using an on-path attacker”). RDP needs to be hardened against attack to reduce the risk of exploitation.
Security awareness training is about making people part of the solution. Strong cyber security isn’t just about technology; if people aren’t aware of risks and how to avoid them, technological defences can be bypassed. Using weak passwords, opening phishing emails, and not updating software are a few common causes of security incidents that can be covered in security awareness training.
How can Think IT help with cyber security?
At Think IT we have a high level of cyber security expertise, to CISSP level, and we support many clients with all areas of cyber security.
Looking at the areas above, specifically, there are lots of things we can do to help.
Updating software:
It’s important that software is kept up to date; attackers often find weaknesses in things like operating systems and applications, and develop attacks to take advantage of them.
Fortunately, the software vendors are also finding weaknesses, as well as monitoring for those that attackers have found, and creating fixes to address them.
Some software, including the common operating systems, support ‘automatic updates’, so the system checks whether any updates are available (and downloads them, if there are any) without you having to. At the bottom of the page are instructions and links to update and/or enable automatic updates on a range of platforms.
These settings will help to ensure that the operating system and some of the key applications are kept up to date.
There are lots of software items that aren’t covered by these routines, of course. At Think IT we have a ‘remote monitoring and management’ process that allows us to keep an eye on the status of each device, and to remote update software when the vendors release patches. Just get in touch with us if you’d like to talk about this. Updating software regularly is also increasingly a requirement (e.g., for Cyber Essentials, cyber risk insurance etc.) and this process can help with compliance.
Multi-Factor Authentication (MFA)
As mentioned above, MFA is also becoming a widely-recommended security control, and a common requirement in standards, compliance, insurance etc.
It can be applied to many system access processes, but it is generally seen as most important for:
- Online financial processes
- Access to cloud email services
- Remote access to business networks
For the first one, online banking already, in most cases, requires MFA: a code sent by text message to a phone, or obtained from a card reader, is needed in addition to the username and password.
Protecting email services is important because of the sheer number of attacks that involve email, and the impact if a business email account is accessed by an attacker. Microsoft 365 is the main platform used by SMEs for email (as well as many other services), so this is the one we’re mainly focussed on.
Microsoft have an MFA solution for Microsoft 365, and there’s some information about it on the Microsoft Support site. Think IT can set this up for your Microsoft 365 accounts, so just get in touch with us if you’d like us to put this in place for you.
If you also have remote access to business systems (such as servers or desktops in your office), this is another area to look at. We can provide a great value, market-leading MFA solution to protect RDP from password attacks. There’s more information about this on the MFA page of the Think IT website, or get in touch with us and we’ll run through it.
Secure Remote Access
As we’ve said above, remote access does create some additional cyber security risk; after all, if it wasn’t possible to remotely access a system, an attacker would have to get physical access to it in order to attack it.
Aside from avoiding use of remote access (which as we covered, isn’t palatable for most organisations), there are two main ways of managing this risk:
- Adding security measures to address weaknesses in the RDP approach: our Think IT RDP security insights article breaks this down, step by step.
- Replacing RDP with a remote access solution that is more secure by default: our Think IT insights article on secure remote access with Splashtop explains this in more detail.
If you need to check or improve your remote access security, just get in touch with us.
Security Awareness Training
Whilst technical controls are important in cyber security, there are others too:
- Physical controls: preventing unauthorised physical access to systems and data
- Administrative, or management controls: policies, processes and people, that create a strong cyber security posture.
Security awareness training is an administrative control; by raising awareness of the risks, people are better able to defend themselves and the systems and data they use.
Key areas to focus on are passwords, malware (and ransomware specifically), phishing emails, and updating software.
We can deliver effective security awareness training for individuals and teams, and we build in helpful hints and practical tips that can be used at home and shared with others, as well as used in the workplace, as we find this engages people more. If you want to talk about security awareness training, just get in touch with us.
Software Update Instructions and Links
Microsoft Windows Devices
- Operating system: by default Windows 10 and 11 are configured to update automatically: https://support.microsoft.com/en-us/windows/manage-updates-in-windows-10-643e9ea7-3cf6-7da6-a25c-95d4f7f099fe
- Applications: the Windows platform supports applications from thousands of vendors without a unified update vehicle. Some applications can be automatically updated through the Microsoft Store: https://support.microsoft.com/en-us/windows/turn-on-automatic-app-updates-70634d32-4657-dc76-632b-66048978e51b. For other applications, the relevant vendor process will need to be followed.
- Browsers: the process for updating browsers varies depending on the browser(s) used.
- Productivity (e.g., ‘Microsoft Office’) software: where Windows and Microsoft Office are used, a system can be set to update Office at the same time as the Windows operating system: https://support.microsoft.com/en-us/office/update-office-with-microsoft-update-f59d3f9d-bd5d-4d3b-a08e-1dd659cf5282. For different office packages, or non-Windows operating systems, perform an internet search for the update process for the relevant office package.
Apple macOS Mobile Devices
- Operating system: https://support.apple.com/en-gb/guide/mac-help/mchlpx1065/mac
- Applications: the macOS platform supports applications from many vendors without a unified update vehicle. The relevant vendor process will need to be followed.
- Browsers: the process for updating browsers varies depending on the browser(s) used.
Android Mobile Devices
- Operating system: https://support.google.com/android/answer/7680439?hl=en-GB
- Apps: https://support.google.com/googleplay/answer/113412?hl=en-GB
Apple iOS and iPadOS Devices
- Operating system: https://support.apple.com/en-gb/guide/iphone/iph3e504502/ios
- Apps: https://support.apple.com/en-gb/HT202180